Playing with computers since age 13, time to start documenting all the wonderful things and treasures I have discovered and developed - also a blog to serve as a time-saver by not having to reinvent the wheel.
Search
Thursday, December 17, 2020
Raspberry Pi Wireless Wi-Fi TOR Anonymizer Gateway (Yet Another Post)
Friday, December 4, 2020
PCVMS - taking the aspirational DOS based VMS inspired multitasking environment for a spin
According to a smattering of information on the internet, there was once a computer software company called Wendin based in Cheney, WA. They launched a product called PCVMS "Personal Operating System" in 1985. It was distributed on a set of three 5.25" 360KB floppy diskettes. More history and juicy bits are in Bill's 2009 post in his "Personally Interesting Stuff" blog. I also found a public profile of Steve Jones at Linkedin, "Steve launched Wendin's Computer Systems Division in 1984, developing the XTC text editor, the PCVMS operating system ("a VAX/VMS operating system clone that ran on IBM PC/ATs), the PCUNIX (later called PCNX) operating system (a Unix clone that ran on IBM PC/ATs), Operating System Toolbox (an operating system toolkit that enabled software developers to create their own operating systems), and Wendin-DOS (an MS-DOS clone with OS/2-like screen groups and multitasking), among other products." The March 1997 issue of IEEE Software "New Product Reviews" contains a quick review of PCVMS written by Randy Kaplan of Temple University:
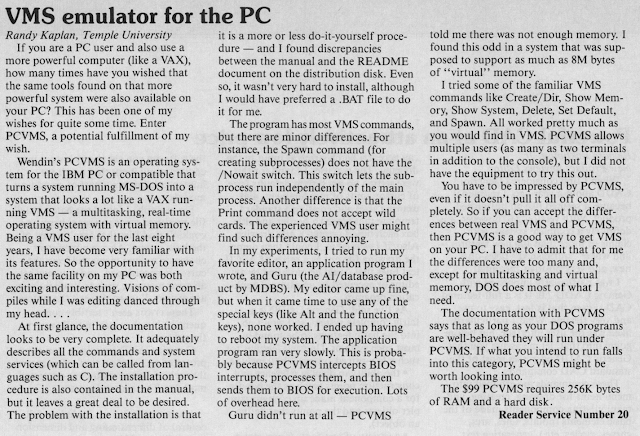 |
R. Eckhouse, "New Product Reviews" in IEEE Software, vol. 4, no. 02, pp. 79-84, 1987.
doi: 10.1109/MS.1987.230374
keywords: {null}
url: https://doi.ieeecomputersociety.org/10.1109/MS.1987.230374 |
A trademark was apparently refused for "PCVMS" in 1986. It was described in the trademark application in 1985 as "MAIL ORDER COMPUTER PROGRAMS USED BY OWNERS OF PERSONAL COMPUTERS IN PERSONAL COMPUTERS AS OPERATING SYSTEMS PROGRAMS FOR THE GENERAL OPERATION OF SUCH PERSONAL COMPUTERS". In any case, a"VAX/VMS operating system clone that ran on IBM PC/ATs" is intriguing. Responses to my quick questions at the HECnet mailing list and comp.os.vms NNTP group indicate folks already played with PCVMS decades ago. However, the universal opinion seems to be PCVMS should be approached with tempered expectations.
I fired up a 86BOX instance running Caldera DR-DOS 7.03 on a 80486SX 25MHz PC and installed PCVMS 1.08 following the instructions in the PCVMS README file. On launching PCVMS, it asks for a username and password. Username "root" with empty password presented a welcome message and a "$" command prompt.
There is VMS-like help, one of the installed files even being HELPLIB.HLB like in DEC VAX VMS systems. On the other hand, the PCVMS user authentication system is straight off Unix, relying on a "passwd" file under "etc" directory under the boot drive. The touch of Unix probably has something to do with "PCNX UNIX-like environment; not just UNIX-like tools, but multi-processing under MS-DOS" which provided at, cat, cmp, cp, cron, date, df, echo, false, file, find, finger, getty, grep, group, grppswd, head, kill, line, logname, lpd, lpr, ls, mail, mkdir, mkgroup, mkuser, more, mv, news, nice, nohup, od, passwd, pr, ps, rev, rm, rmdir, rmgroup, rmuser, sh, sleep, strings, stty, tail, tee, test, time, touch, true, tty, uniq, wc, who, whodo, write.
By the way, I also briefly tried Wendin's "Wendin-DOS multitasking, multiuser MS-DOS replacement" which is publicly available, but it kept crashing with some sort of internal error in a rectangular box occupying the top third of the screen. This is another operating system that is my queue of things to explore further.
But, at this point, it appears for using "multi-user" features of PCVMS we need some sort of multiple hardware terminal connections with each then becoming a session. Something to be tried if and when I come back to this. A manual would be nice, but so far I have none.
Thursday, December 3, 2020
Command Line Torrent Client and Gopher Server on Raspberry Pi
One Raspberry Pi in my home lab has a 1TB USB external hard disk drive connected to it. I wanted to share some retrocomputing hobbyist-related stuff publicly in gopherspace. I also wanted a command-line torrent client to download retro public-domain stuff from archive.org and other places. Here are the pieces I ended up using.
GOPHER
I set up a gopher server on the Pi and opened up and forwarded TCP/IP Port 70 to it. I am able to reach the gopher server using a standard web-browser from the public internet using Floodgap Gopher-HTTP Gateway. Currently it has some ancient ZX Spectrum home microcomputer stuff. It is connection-rate limited using UFW, so slow down while visiting it to not be refused!
Floodgap also runs a great Veronica-2 Gopherspace Search engine.Here are the steps for quickly getting into Gopherspace:
Gopher server
pygopherd: PyGopherd is a modern Internet Gopher server written in Python and is maintained by John Goerzen. In addition to support for RFC 1436 Gopher and Gopher+, PyGopherd also supports HTTP and WAP (Wikipedia).
Gopher client (browser) - Text/Terminal
Good old Lynx terminal web client continues to support Gopher. It is available from standard package repositories for virtually every operating system in use.
Gopher Client (Browser) - Windows, Mac OS X
Little Gopher Client - works great, available for MacOS X, Linux and Windows.
Command-line bittorrent client
rtorrent works fine!
Recommended Products from Amazon